Well it has been good start to our 6th year in business. We would like to thank all our customers and partners both old and new who are contributing to our success. Without you we do not exist and most importantly get to build stronger more secure companies and products for our clients.
I wanted to bring your attention that on Feb. 7th I will be in Toronto to give a presentation to CIA Plus. My topic will be about IoT Challenges and Issues and Standards. If your in the Toronto area this evening please drop by and join our open discussion on security and IoT.
I will be joined by on my panel with Sangam Manikkayam of Symantec, Bob Martin of Cisco and Victor Garcia of the Schulich School of Business. It will be very informative if you or your organization are considering IoT projects this year. I will provide the security and privacy aspects you should consider when planning or getting ready to launch a new IoT project. If you are able to attend more information can be found here: https://www.meetup.com/CIA-Plus-TO-the-business-of-Cloud-IoT-and-Analytics/events/236370120/
In the meantime, if you have any security questions or concerns for IoT please do not hesitate to reach out to us.
Updated: Feb. 13, 2017
I would to take this opportunity to thank all of those that came out on an icy night in Toronto to the CIA Plus Meet Up. My only regret was the lack of time to discuss all the topics in depth. We did have some good discussion after in the networking portion of the meeting and key topics of discussion worth mentioning are how does one who has no experience in security and privacy conduct threat modeling? The other is finding the resources necessary to support these projects.
While there is publicly available information on threat modeling, you may have need to find a cyber security partner or consultancy that has this expertise in these areas to help you with a project to teach you approach, tools and train your staff. They should be able to provide the baseline elements to implement these aspects in your organization including the after project support, should you required it.
The second point about security resources is a bit more difficult as the number of technical security experts for IoT is limited. If you are looking to hire a security resource(s) look for reference-able projects that include aspects of technical architectures in mobile, cloud and distributed systems. Experience in these key areas will provide the necessary basis to conduct risk assessments against IoT architectures.
As discussed please find the following:
1. A copy of the presentation
2. A IoT mind map
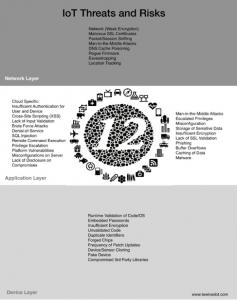
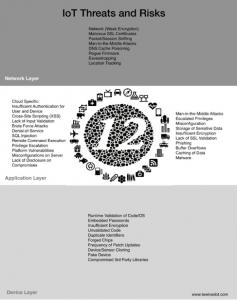
3. The threat poster
Also please find an article from reporter, Denis Deveau, who was in the audience. Thank-you Denise for the coverage of this event.
 CIA Plus – Feb 7 – Final SWG_5_IoT_Technologies_MindMap
CIA Plus – Feb 7 – Final SWG_5_IoT_Technologies_MindMap